The architecture of
At Yangtze Data Lab, we do not simply process information. We apply a rigorous, multi-stage filtration and validation framework designed to isolate high-signal drivers from the noise of the Malaysian market.

Signal Fidelity Index
Our proprietary metric for measuring the reliability of predictive outcomes before delivery.
Our commitment to methodological rigor is absolute.
"Data is only as valuable as the skepticism applied to it. We build models that survive stress, not just historical fit."
Dynamic Bias Neutralization
Machine learning models often inherit the prejudices of their training data. Our data lab implements an "Adversarial Bias Audit" on every predictive model. We simulate unconventional market shocks to identify if the model relies on correlations that are fragile or socially skewed, ensuring outcomes are both ethical and mathematically robust.
Contextual Localization (The KL-Standard)
Standard global analytical frameworks often fail to account for the nuances of the Malaysian logistics, retail, and financial landscapes. Our research standards mandate the integration of local macroeconomic signals, from Ringgit volatility to regional supply chain bottlenecks, providing a localized logic that synthetic models miss.
Atomic Verification Pipeline
Before a data set is ingested into our predictive laboratory, it undergoes 14 distinct validity checks. From timestamp synchronization across disparate sensors to outlier isolation using modified Z-scores, we ensure that the "raw material" of your data is structurally sound before expensive processing begins.

Precision is not an accident.
Every byte of data at Yangtze Data Lab is treated as a critical asset, protected by encryption and verified by redundant validation cycles.
Ethics in the Age of Autonomy
Data science without ethics is a liability. At Yangtze Data Lab, our research standards extend beyond mathematical accuracy into social responsibility. We operate under three non-negotiable ethical pillars:
Privacy by Design
We employ k-anonymity and differential privacy protocols to ensure individual identities are never exposed in aggregate trends.
Explainability
No "black boxes." We prioritize models that can be interpreted by humans, allowing stakeholders to understand the 'Why' behind every 'What'.
Data Sovereignty
Respecting geographic data boundaries. All data processed for Malaysian entities stays compliant with local PDPA regulations.
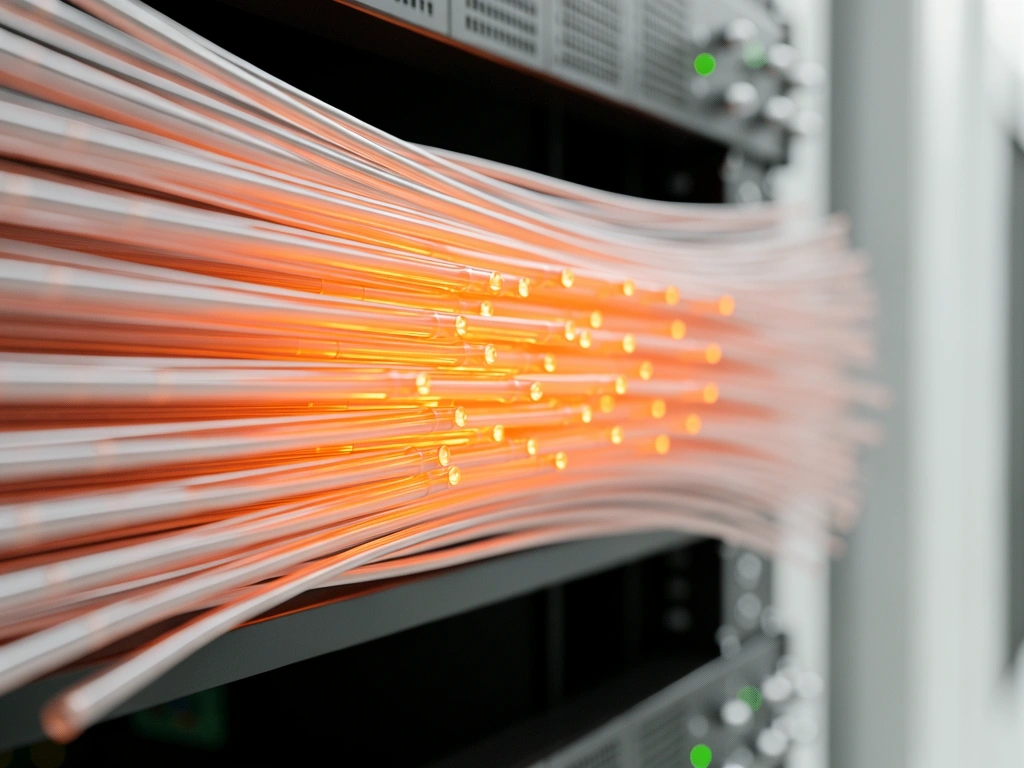
Our Laboratory Infrastructure
High-signal data isn't just about software; it's about the environment where it lives. Our KL-based servers are temperature-controlled and protected by biometric security, ensuring the physical integrity of your primary data assets.
-
Redundant N+1 Cooling & Power
-
Air-Gapped Secure Calculation Zones
-
24/7 Threat Monitoring & Penetration Testing
Ready for a higher standard of insight?
Discover how our research protocols can be applied to your specific business challenges. Our senior lead analysts are available for methodology deep-dives.
99.8%
Model Stability Rating
0.02ms
Ingestion Latency
ISO 27001
Framework Compliance